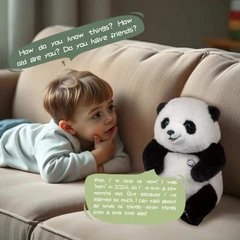
How to Protect Children's Data Security When Using Connected Toys?
With the rise of smart toys, many now feature internet connectivity-voice interaction, remote control, data syncing, and more. However, these functions also pose privacy leaks and cybersecurity risks. As a parent or guardian, how can you ensure your child's data security? This guide provides actionable steps to safely use connected toys.
1. Why Do Connected Toys Pose Security Risks?
Smart toys often require Wi-Fi, Bluetooth, or companion apps, which may involve:
✅ Data breaches: Toys may collect sensitive information like voice recordings, location, and usage habits.
✅ Hacking risks: Unencrypted communication could allow malicious control (e.g., hijacked cameras).
✅ Third-party tracking: Some apps or cloud services share data with advertisers.
Real-World Cases:
In 2017, Germany banned a smart doll over privacy concerns due to potential eavesdropping.
Vulnerabilities in certain kids' smartwatches allowed remote location tracking.
2. How to Secure Internet-Connected Toys
🔹 1. Choose Compliant, Secure Toys
Look for international certifications (e.g., EU GDPR, U.S. COPPA).
Prefer reputable brands over cheap, unknown smart toys.
🔹 2. Adjust Privacy Settings & Permissions
Disable unnecessary features: Turn off microphones, cameras, or GPS if unused.
Review privacy policies: Ensure toy companies don't sell data to third parties.
🔹 3. Secure Your Home Network
Use strong passwords: Avoid default Wi-Fi passwords; update regularly.
Enable firewalls/VPNs: Block external intrusions.
Set up a kids' guest network (supported by some routers).
🔹 4. Regularly Update Firmware & Apps
Manufacturers release patches; keep toys and apps up to date.
🔹 5. Supervise Usage
Monitor playtime with connected toys.
Teach kids not to share personal details (name, address, etc.).

Advanced Protection: Technical Measures
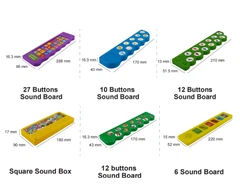
Our company's AI products have all taken safety measures to enable children to better enjoy the use of technology and safety
For Manufacturers
End-to-end encryption (e.g., TLS 1.2+).
Anonymized data-replace IDs instead of names.
Embedded security chips (e.g., TPM)